How TLS Works to Secure Your E-Commerce Website
If you run an e-commerce website, your site could have serious vulnerabilities if its protocols are running on Secure Sockets Layer (SSL) or older versions of Transport Layer Security (TLS). Yes, SSL was the standard encryption protocol for 20+ years but it is no longer the standard. Unfortunately, there are a number of security vulnerabilities with SSL and even with its newer counterpart, TLS.
Protocols are not the same as Certificates
Before you call your webmaster or IT department, we should point out that there is a difference between an SSL certificate and an SSL protocol. Certificates are small data files that bind your cryptographic key to your information. You need a certificate that works with your protocol but the two are not the same. We are used to hearing the phrase “SSL Certificate,” but it actually should be called a “certificate that works with SSL.”
You still need an SSL certificate. It’s the protocol you should be worried about.
You may have received an email similar to this one from your chosen payment gateway provider about no longer supporting TLS 1.0 and 1.1.
Dear Authorize.Net Merchant:
After discussions with many of you regarding the effort and timelines required for updating your payment systems to disable TLS 1.0 and 1.1, Authorize.Net has decided to extend our deadline from September 18, 2017. The new date for when we will no longer allow TLS 1.0 and 1.1 is February 28, 2018.This extension will provide you with additional time and allow you to continue processing through the upcoming holiday season before any changes are required. It also still allows Authorize.Net to meet the PCI DSS requirements to disable early TLS by 2018.
However, we still strongly encourage you to update your systems as soon as possible. Please refer to our TLS FAQs for additional information regarding TLS disablement.
Here’s what you need to know about about TLS and your e-commerce website security.
What is TLS?
TLS is a different security standard that uses stronger encryption algorithms than SSL and works on different ports. TLS establishes a secure communications channel between two systems that are trying to communicate with each other and then protects the information passing from one system to the other using a cryptographic protocol. There are three versions of TLS – 1.0, 1.1 and 1.2. Unfortunately, hackers have uncovered several vulnerabilities in versions 1.0 and 1.1, and there are no files or patches that can fix their vulnerabilities. So, if you want to make sure your servers are secure, you need to switch to TLS 1.2.
What you need to do
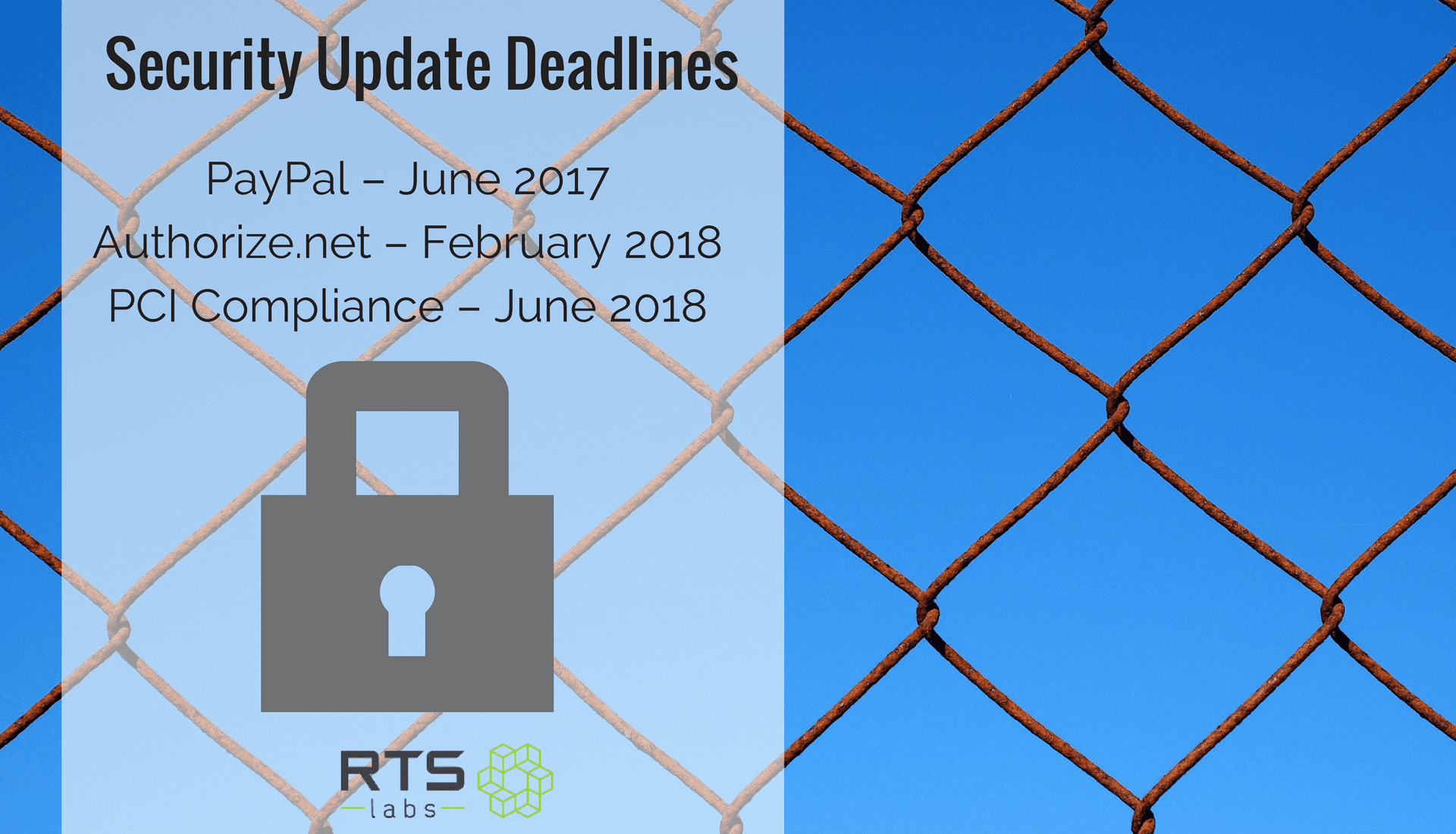
Running on SSL, TLS 1.0, or TLS 1.1 is so risky that it is no longer going to be considered PCI compliant. That’s why big names like Authorize.Net and PayPal are making adjustments and warning users. What these warning notifications mean is that you need to confirm that your site is using TLS 1.2 by their given deadlines:
- PayPal – June 2017
- Authorize.net – February 2018
- PCI Compliance – June 2018
You can start by running an SSL/TLS Server Test on your website to confirm which versions you’re running on your server. This will give you a rough idea of whether or not you need to take further action. From there, you’ll need to contact your webhost to ensure that TLS 1.2 is enabled on your server. If your host is PCI compliant, they should have it enabled already, but we recommend double checking.
If you don’t confirm that you’re running the correct protocol by the due dates listed above and it turns out your site is using the older versions, your users may experience problems. Beyond users having problems, if the security of your site is compromised, that means your client data can be compromised. Data breaches are not only extremely costly, they can ruin your credibility and trust. Just ask anyone at Equifax, Wells Fargo, Home Depot, Deloitte, Target …
Wondering how secure your website and systems actually are? We’re happy to answer your questions. Reach out to us at RTS Labs for guidance about e-commerce and security for your website.